Explore the evolution of fraud prevention, understand the limitations of traditional methods, and learn how advanced frameworks can better mitigate risks.
Contents
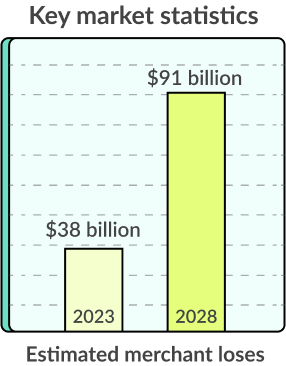
While we have made substantial advancements in identifying, mitigating, and preventing fraud, it’s an ongoing — and growing — battle. Juniper Research reports that merchant losses due to fraud in 2023 will account for $38 billion and will continue to escalate, reaching, as forecasted, $91 billion by 2028.
The stakes are high, and fraud actors are becoming more sophisticated. Criminal syndicates and state actors are increasingly behind fraudulent activity with deep resources and advanced technology. Effective fraud prevention requires a similar commitment.
In this article, we’ll discuss the evolution of fraud prevention, how traditional methods have significant limitations, and how advanced fraud risk prevention frameworks can help you mitigate risk.
The evolution of fraud prevention
As fraud prevention approaches have evolved, the limitations of traditional prevention programs have become more evident. Traditional approaches have combined internal controls, risk management, and compliance to detect, prevent, and mitigate fraud risks. These are all important components of fraud prevention. However, the inherent limitations can pose challenges.
Drawbacks of traditional approaches to preventing fraud
While the Association for Financial Professionals (AFP) shows that attempted or actual fraud grew at a lower rate in 2022 than in the past eight years, 65% of organizations surveyed said they were victims of attempted or actual financial fraud.
“Sixty-five percent of respondents indicate that their organizations were victims of either attempted or actual fraud activity in 2022 – the smallest percentage since 2014.”
Internal controls
Internal controls are crucial in fraud prevention, but there are several key concerns with traditional approaches to safeguarding assets and preventing fraudulent activities, such as:
- Over-reliance on manual processes: Manual processing is time-consuming and difficult to scale cost-effectively. They tend to produce more errors and require more effort to constantly evolve as cybercriminals and those committing fraud continue to deploy new tactics.
- Reactive approach: Internal controls typically react to situations when fraud has occurred. They often lack the proactive or predictive tools necessary to identify warning signs and prevent sophisticated fraud schemes.
Risk management strategies
Risk management identifies and mitigates risks that can lead to fraud. However, traditional risk management strategies also have limitations, including:
- Inadequate risk assessment: Traditional risk assessment methods may fail to account for emerging fraud risks.
- Based on historical data: Risk assessments rely on historical data rather than an ongoing risk assessment for future risk. Threat actors can exploit gaps in risk assessments.
- Lack of agility: Traditional risk management frameworks are often rules-based, rigid, and slow to recognize new threats. As such, they may not be equipped to respond promptly as new tactics or technology is deployed.
Compliance measures
Compliance frameworks and procedures are designed to ensure organizations comply with relevant laws, regulations, industry standards, and internal compliance measures. Limitations include:
- Checkbox compliance: Compliance measures generally prioritize addressing minimum regulatory requirements — checking the box rather than focusing on specific risks.
- Not recognizing threats outside of compliance: Traditional compliance measures only focus on fraud schemes that impact compliance and often do not address tactics or warning signs outside the regulatory scope, including internal and external fraud risks.
False positives
False positives are a continuing concern with KYC/AML compliance. Traditional approaches tend to surface significant false positives, requiring a time- and resource-intensive manual review. New AML regulations are increasing the monitoring with reporting and cracking down on companies that are not addressing high levels of false positives.
Limitations of traditional solutions include:
- Inflexible or coarse-grained rules that detect scenarios that are not suspicious
- Using subsets of event types and data to limit the signals used in detection.
Embracing innovation with a proactive mindset
Overcoming these limitations requires adopting more modern and proactive measures for fraud prevention. Such an approach should include:
- Advanced analytics and data-driven decisions
- Real-time monitoring systems
- Regular updates to identify emerging threats
- Regular fraud risk assessments
- Continuing education and training
The Financial Action Task Force (FATF) focuses on best practices for countries to tackle fraud and illicit financial flows. FATF recommends modern, proactive approaches to detecting, preventing, and mitigating fraud. By embracing technological advancements, organizations can remain compliant while enhancing risk prevention measures in several different ways, including:
Data integration and analysis
Businesses need a more holistic view of customers. They can get it by integrating diverse data sources, such as updated transaction records, customer data, employee information, and external data feeds. Accurate and timely data, combined with advanced analytics featuring predictive modeling and machine learning (ML), can better uncover patterns and suspicious activities indicative of fraud.
Algorithms help identify correlations between actions that are precursors to fraud that manual processes would likely never be able to identify.
Fraud detection models
When ML is trained on historical fraud data and infused with evolving threats, users can develop predictive models more adept at identifying potential fraud. When models provide continuous real-time data analysis, they can immediately warn by flagging activities or transactions that display signs of potential fraud.
With automation, fraud detection models can help businesses identify and prevent fraud more efficiently.
“Over half of organizations with annual revenue of less than $1 billion were unable to recover funds lost due to payments fraud attacks.”
Network analysis
Identity verification alone doesn’t prevent fraud. Another area where technology can make a significant difference is the analysis of underlying relationships and connections between entities. Network analysis can identify complex relationships among customers, suppliers, business partners, and employees to uncover fraud schemes, such as money laundering or collusion.
Behavioral analysis
Establishing baselines for normal behavior and defined thresholds makes it easier to detect deviations or anomalies. An example would be when an employee accesses sensitive data that is unrelated to their job function or bypasses the authentication and access controls. Another flag might be someone changing data that normally remains static. These events may indicate potential fraud, data theft, or compromised credentials allowing threat actors to access or manipulate data.
Behavioral analysis is also key in analyzing customer purchasing patterns and account activities to identify potential fraud.
Real-time monitoring
Today, real-time monitoring can continuously track activities and provide instant alerting for suspicious behavior. This enables businesses to take immediate action to prevent fraud in progress and/or minimize potential losses. Artificial intelligence (AI) and ML can help process large volumes of data in real time, allowing for more comprehensive monitoring and fraud detection.
Data sharing and collaboration
Data can be shared among other organizations, government agencies, and industry groups by masking identities. Sharing anonymized fraud data can help identify new patterns and evolving trends across multiple organizations, leading to more effective fraud prevention tracking for everyone involved.
Fraud risk assessment
Streamlining and automating fraud risk assessments help identify gaps in fraud detection and prioritize resources for mitigation. Technology and data analytics can enhance fraud prevention, but organizations should not rely solely on technology alone. Skilled fraud investigators, human reviews, and continuous awareness and detection training remain crucial to interpret technology outcomes and ensure compliance.
Technology can automate much of the process and augment fraud detection, prevention, and mitigation, but it requires regular reviews, such as fraud risk assessments.
Assessing and managing fraud risks
Conducting comprehensive fraud risk assessments, identifying potential vulnerability, and prioritizing risks are essential to a holistic fraud prevention approach. Organizations should undertake a comprehensive fraud risk assessment and update it regularly to maintain current and account for evolving fraud tactics. Organizations should deploy a customer identity platform that provides advanced capabilities for identity verification, screening and compliance, and fraud detection and prevention.
Conducting fraud risk assessments and using a customer identity platform (CIP) provides significant benefits, which can be enhanced by implementing these best practices.
Establish assessment objectives
Companies need to define the scope of their fraud risk assessment, including the areas and processes to evaluate. Customer onboarding, account management, and transaction processing are common areas to assess, but analyzing end-to-end processes for managing financial and customer data is also essential.
Assemble a cross-functional team
Creating cross-functional teams with experience in different areas, such as finance, legal, IT, operations, and customer experience, provides a different perspective. Each team member will have expertise in systems and processes in different ways, so they can help provide a fuller evaluation.
Identify key fraud risks
While there are industry standards, every organization has different thresholds and levels of fraud risks relevant to their organizations. Companies must review historical fraud analysis, industry research, benchmarking against industry and competitors, and gain insight from interviewing key stakeholders. This process should include reviewing internal and external factors that can continue to risk.
Assess internal controls
A comprehensive fraud risk assessment needs to examine existing internal controls and how effective they are at mitigating fraud risk. The assessment should evaluate control activities, such as:
- Access controls: These security measures restrict user access to authorized resources based on roles and privileges.
- Authentication mechanisms: These are methods used for verifying users’ identities before granting access, such as passwords, biometrics, and multi-factor authentication (MFA).
- Transaction monitoring: This refers to continuous surveillance of financial activities to identify and prevent potential fraud or suspicious behavior.
- Segregation of duties: This divides critical tasks among different individuals to reduce the risk of fraud and errors and enhance accountability.
Internal controls often contain vulnerabilities that fraudsters can exploit and may be difficult to uncover because they have existed for some time. Yet, platforms, systems, and networks continue to evolve, as do fraud schemes. Analyzing legacy processes and technology can help find vulnerabilities that may not be visible in day-to-day operations.
Evaluate fraud detection and prevention measures
Beyond internal controls, an assessment of organizational fraud detection and prevention measures is necessary, including:
- Fraud monitoring systems: These are designed to monitor and track activities to detect and prevent fraudulent behavior.
- Data analytics capabilities: These help analyze and interpret large volumes of data to uncover patterns, trends, and insights.
- Rules engines: These apply predefined rules and logic to data and transactions to identify potential fraud based on customizable criteria.
- Anomaly detection mechanisms: They help identify deviations from normal patterns of behavior or transactions, which can indicate potential fraud
A fraud risk assessment helps identify and prioritize areas where enhancement is required to improve risk posture.
Integrate a customer identity platform
A comprehensive customer identity platform is foundational to modern fraud detection. CIP provides multiple benefits to reduce fraud, including:
Enhanced identity verification
Robust identification verification includes techniques such as:
By employing advanced identity verification, you can help ensure customers are who they claim to be and reduce the risk of fraudulent identities.
Risk-based authentication
A customer identity platform can also deploy risk-based authentication analyzing various datasets to assess risks. Such data includes:
- Behavioral analytics: This analyzes user behavior patterns to detect potential fraud or security threats based on abnormal actions.
- Device intelligence: This refers to assessing a device’s trustworthiness and risk level by analyzing data such as device type, location, and usage patterns.
- Contextual data: This includes additional information about a user’s environment and activities used to make informed risk-based decisions.
Different levels of security measures can be deployed based on the perceived risk associated with each customer or transaction. For example, location intelligence can detect VPNs, proxies, and geo-restrictions or scrutinize transactions at different thresholds in locations more prone to fraudulent activity.
Fraud detection and monitoring
ML algorithms and real-time monitoring can detect patterns that indicate fraud at a much higher level than traditional and manual reviews. By continuously analyzing transaction history, customer behavior, and contextual data, CIP solutions can identify suspicious activity and potential fraud at scale.
Adaptive authorization
The right customer identity platform can adapt, enabling dynamic access controls based on risk profiles associated with each customer or transaction. Dynamic controls based on preconfigured or manual control limits help prevent unauthorized access and reduce risk.
Quantify and prioritize risks
You can also assign risk ratings to identify fraud risks based on the potential impact and likelihood of occurrence. This helps prevent false positives while ensuring events that pose the greatest threats are flagged for review with customizable risk scoring.
Develop mitigation strategies
As risks are uncovered, cross-functional teams can develop strategies to address each fraud risk. Leveraging the insights of the customer identity platform to enhance existing controls, improve response mechanisms, and implement additional fraud prevention measures
Document and communicate
The insights from fraud risk assessment must be documented and communicated to team members and stakeholders, including identified risks, risk ratings, and recommended mitigation strategies. Sharing results helps foster transparency and buy-in for any remediation efforts.
Ongoing monitoring and review
Risk assessment is not one-and-done. Organizations need an ongoing monitoring process to assess fraud mitigation efforts and mitigation strategies’ effectiveness. Regular reviews and updates are necessary to account for emerging risks, compliance and regulatory updates, and advancements in fraud detection.
Developing an advanced prevention framework
Businesses can enhance their ability to identify and prevent fraudulent activities in real-time, reduce false positives, and improve overall operational efficiency in managing fraud risks by leveraging advanced analytics and AI for fraud detection. An advanced fraud prevention framework will streamline operations, improve efficiency, and reduce manual work in managing fraud detection, incidents, and analysis.
Fraud risk assessments, analysis of past incidents, and employing industry best practices can help foster a culture of innovation and agility that is crucial amid today’s continuously evolving threats.
Moving to a modern, advanced fraud detection and prevention framework requires choosing the best fraud detection and prevention software and integrating it into your existing workflow. A partner like MetaMap can help you deploy an advanced fraud prevention framework with proven strategies for reducing fraud. MetaMap ensures compliance with global regulations, leveraging LATAM’s largest pool of data sources and customized verification flows that integrate with your workflows.
For more information on how MetaMap can help mitigate fraud, we invite you to watch our webinar on Layering Fraud Detection Techniques to Reduce Identity Theft. This session will provide techniques to mitigate identity theft and reduce fraud in your operations. Don’t miss this opportunity to deepen your understanding and equip yourself with the tools to navigate today’s complex fraud landscape.
Related content
Subscribe to the newsletter and stay up to date with promotions, special offers and news